How To Install Fail2Ban On CentOS 7
Brute force attacks are a way for malicious hackers to get access on your machine so in order to protect from these kind of attacks you need to prepare. A very good solution is the use of an intrusion prevention framework on your server such as Fail2Ban which will provide security on your server by blocking and banning the ip address from which the attack is coming from.
Experiencing ssh attacks on your server is a real struggle and I am sure you don’t want to be part of that so better follow the instructions on this tutorial in order to be prepared for the future.
What Is Fail2Ban
Fail2Banis a very useful piece of software widely spread in the industry, reduce the rate of incorrect authentications attempts with the main goal of preventing brute force attacks on various services such ssh, apache, courier and many others. It basically scans log files for finding malicious IP addresses with many password failures.
However you should always keep in mind that Fail2Ban does not protect your services from weak authentications so make sure you use strong enough passwords and also two factor or public/private authentication mechanisms.
How To Install Fail2Ban On CentOS
The first step we need to take for installing Fail2Ban on our CentOS machine is to make sure that we have root privileges, the following command will help to login as a user with root privileges.
su root
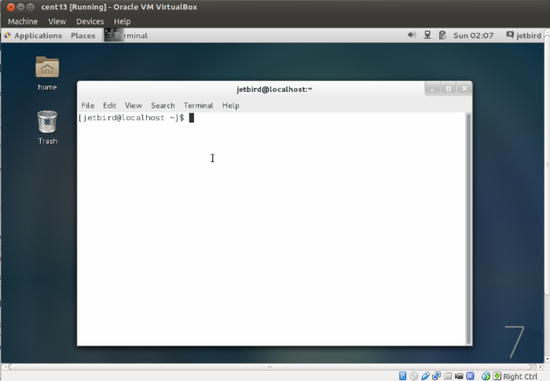
The command for logging as root is shown below.
su root
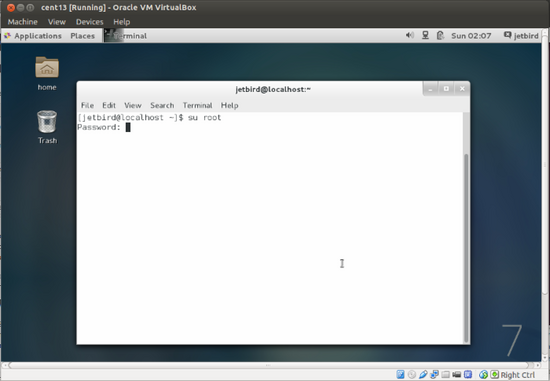
And the prompt changes.
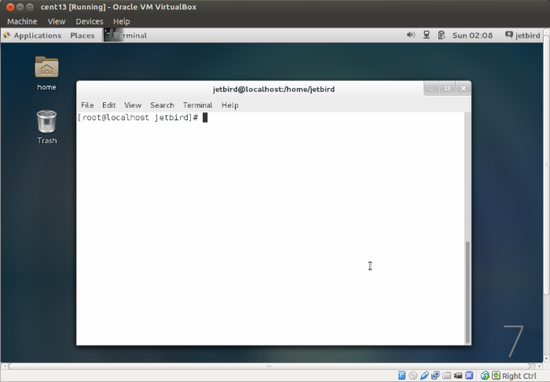
Once the user has gained full privileges on the system guaranteed by being root it is time to get into some real action. The next step consists in installing the epel-release which will help us to install extra packages from EPEL(Extra Packages for Enterprise Linux) on our CentOS machine.
The following command will do the entire job for you.
yum install epel-release
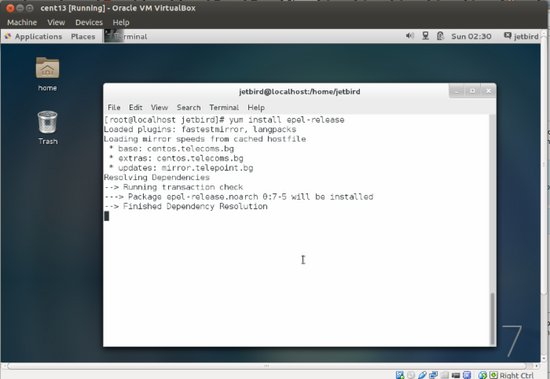
Once the installation is finished you will be gifted with access to alot of new packages.and one of those is fail2ban which can be installed by using the following command.
yum install fail2ban
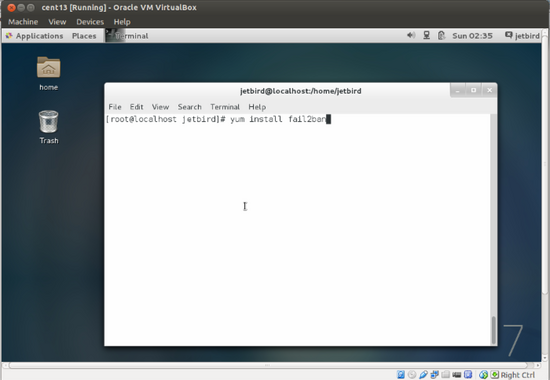
The above screenshot shows the command need to be used in order to install fail2ban on CentOS machines.
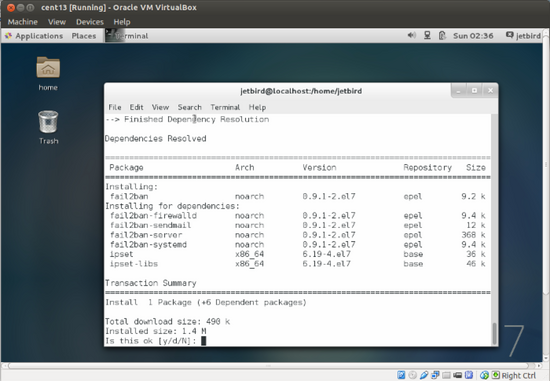
Type y and hit Enter on your keyboard.
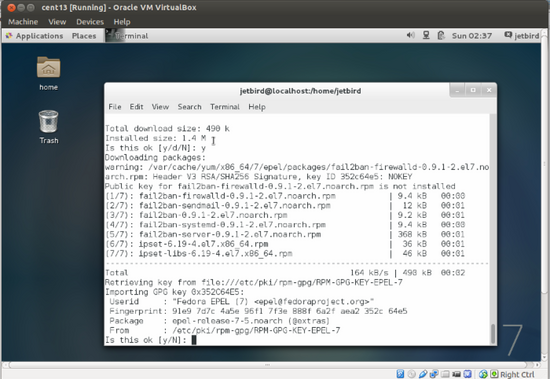
y again.
The installation of fail2ban is finished now.
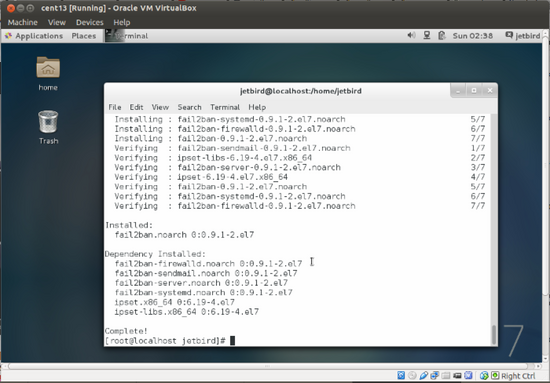
There are also many dependencies being installed such as fail2ban-firewall, fail2ban-sendmail, fail2ban-systemd, fail2ban-server and some others.
A Very Basic Configuration
Fail2Ban is a very complicated tool and requires deep knowledge to be used the right way so instead of explaining it on this tutorial I will do a very simple configuration and then teach you guys how to use it on another tutorial.
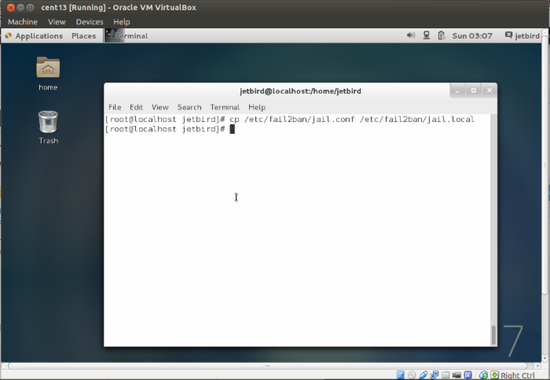
The default configuration for Fail2Ban is kept under /etc/fail2ban/jail.conf but we are not going to directly edit as we don’t want to mess things up at the moment. So create a local copy of jail.conf by using the following command on your CentOS system.
cp /etc/fail2ban/jail.conf /etc/fail2ban/jail.local
Use vim or nano to open the jail.local file like shown below.
vim /etc/fail2ban/jail.local
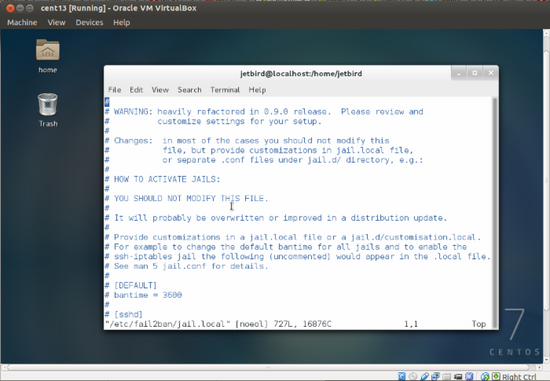
Now scroll down and take a look at options such as maxretry which is the number of failures a user is allowed to have before getting banned, port which specifies port range to be banned, bantime is the number of seconds the malicious user is banned from the service, protocol which is the default protocol being used and a very important option that catched my eye is the ignoreip one.
Every IP address defined here will not be banned by Fail2Ban. This is very useful in case you or other users forget their password and try different combinations to find the right one. Several addresses can be defined using space separator.
Conclusion
In this very detailed tutorial we took a very simple approach on how to install Fail2Ban on CentOS 7 operating system. We also covered a bit Fail2Ban default configuraition file, explaining different options and their usage. In another tutorial we will do a deep exploration of Fail2Ban so you can start mastering the tool for your own good and security.
If you want to use Fail2Ban on Debian based systems, look at the following link.
Source:http://img2.tuicool.com/vUreyaY.png!web





